How do we highlight the risk of a platform, one we use, in a constructive way?
LinkedIn is really good for recon. Project managers like to post updates on new technology deployments, companies post job ads, people are constantly updating their resumes with new skills they have learned from their jobs, and so on.
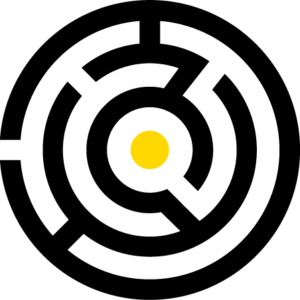
On one project, we were engaged to infiltrate a client using only social media. The diagram below shows how this was achieved (note, this company had a highly active security awareness program).

It was that simple, “hello” to login in two weeks.
Total effort: a couple of hours.
Advanced technical knowledge required: zero.
This is another example of social engineering, given the nature of social media and addictive nature of it, social media platforms are excellent forums for this kind of attack. People want connections, they want “likes”, “shares”, followers. Validation of others seems (for why you want to connect to them) to often come down to the connections they have – “this person has connections, therefore they must be real”. Some people will accept any connection (“The more connections I have the cooler I am!”). These are the initial targets, once you find a few of these you can connect to them, and then fan out from there.
After that it’s a question of how much information can glean from connections without raising suspicion. We have learnt to avoid sending requests to anyone in legal, and IT security folk do tend to be trickier (although not as much as you would think). Marketing people are fantastic, as is anyone in sales.
As the walkthrough above showed, plain old human interaction can go a long way (the request for a date was entirely unsolicited we should add).
So how do you deal with this?
Ban social media use.
Ok so you can’t do that. Social media can be another target for security awareness training, however because of the basic human brain functions these sites stimulate, only a program of constant awareness training stands any chance. People want to be helpful, they want to make friends, and the dopamine buzz from receiving messages and getting likes is extremely powerful for humankind.
Alternatively, counter intelligence (or disinformation programs) can be utilized to pollute information available about your organization on social media. This is difficult given the terms of services of these sites; however, adversaries are unlikely to follow them. So, in the name of protecting your organization, you may want to investigate what can be done.
We’re not saying don’t use LinkedIn, or any social media, but be aware that it’s another conduit into your organization through those who work there and needs to be part of a security plan.